How Pay Factor Authentication Works
AuthLN adds economic control to authentication, requiring real value to initiate protected access attempts. Automated attacks, credential stuffing, MFA fatigue, and proxy abuse become expensive before they ever reach your SOC. No lift-and-shift of your existing IdP.
To users, it’s passwordless.
To attackers, it’s risk.
One Login - Two very different outcomes.
AuthLN adds economic verification to authentication.
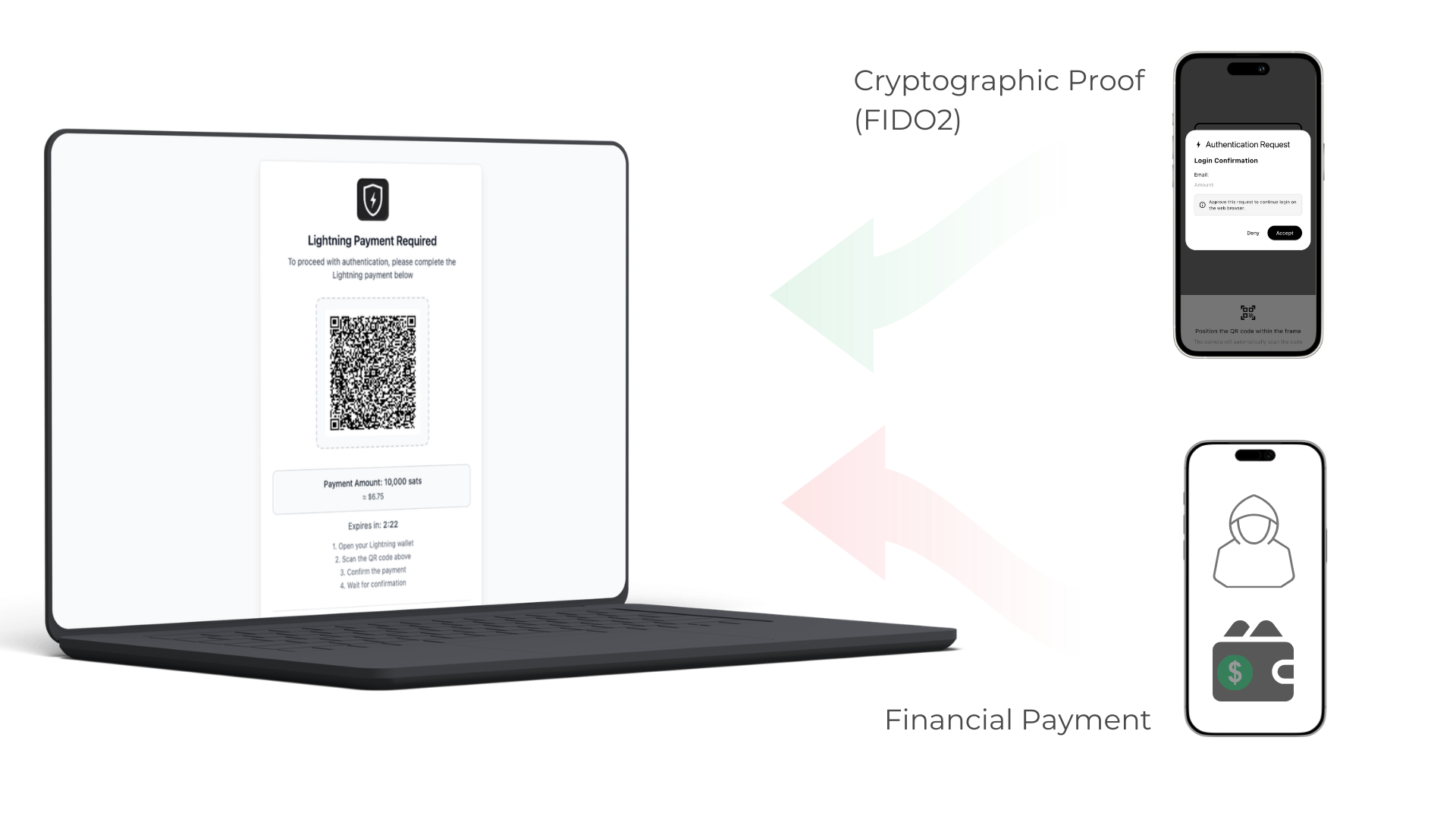
By combining passkeys with a proof-of-work payment challenge, AuthLN allows authorized users to log in normally while forcing attackers to risk real money to attempt access. The result: fewer attacks, stronger identity verification, and a frictionless experience for legitimate users.
Authorized Users satisfy the invoice with a passkey:


Everyone else has to pay…
AuthLN Login Process
User initiates login through the organization’s existing identity provider (Okta, Microsoft, Google, etc.).
AuthLN presents a QR code challenge requesting verification through the AuthLN mobile app.
User scans the QR code using the AuthLN app to confirm device ownership and passkey identity.
AuthLN evaluates the authentication attempt.
• Authorized users automatically cancel the payment challenge.
• Unauthorized users must fund the challenge from their own wallet.
Authorized users proceed normally and are granted access to the requested system or resource.
Unauthorized attempts trigger enforcement. Payment is captured, telemetry is recorded, and the organization’s security policy determines the response.
Request a Demo
Experience authentication that changes the economics of cyber attacks. AuthLN introduces a proof-of-work payment challenge to identity verification, allowing authorized users to log in normally while forcing attackers to risk real money to attempt access.
See how AuthLN integrates with Okta, Microsoft, and Google to strengthen authentication without requiring a lift-and-shift of your identity infrastructure.
Fill out the form to schedule a demo and see how AuthLN can be deployed in your environment.
