Where Passwordless Becomes Enforceable
Smart contracts introduce consequence to authentication — and redefine what identity security can do.
AuthLN combines device-bound FIDO2 passkeys with smart contract–enforced authentication to transform login attempts into contract-governed events.

Device-Paired Authentication (FIDO2 Passkey)
AuthLN leverages FIDO2 passkey architecture to bind authentication to a specific physical device. Each credential is generated and stored inside the device’s secure hardware enclave, preventing credential reuse, phishing replay, or remote impersonation.
How It Secures Access
Device-bound cryptographic keys
Private keys are generated and stored inside the device TPM / Secure Enclave and never leave the hardware boundary.
No passwords to steal or replay
There is no shared secret transmitted over the network. Authentication requires possession of the registered device.
Origin-bound assertions
FIDO2 ensures credentials are cryptographically scoped to the legitimate relying party, eliminating phishing reuse.
Hardware-backed protection
Works natively with Microsoft, Apple, and Android TPM / Secure Enclave implementations.
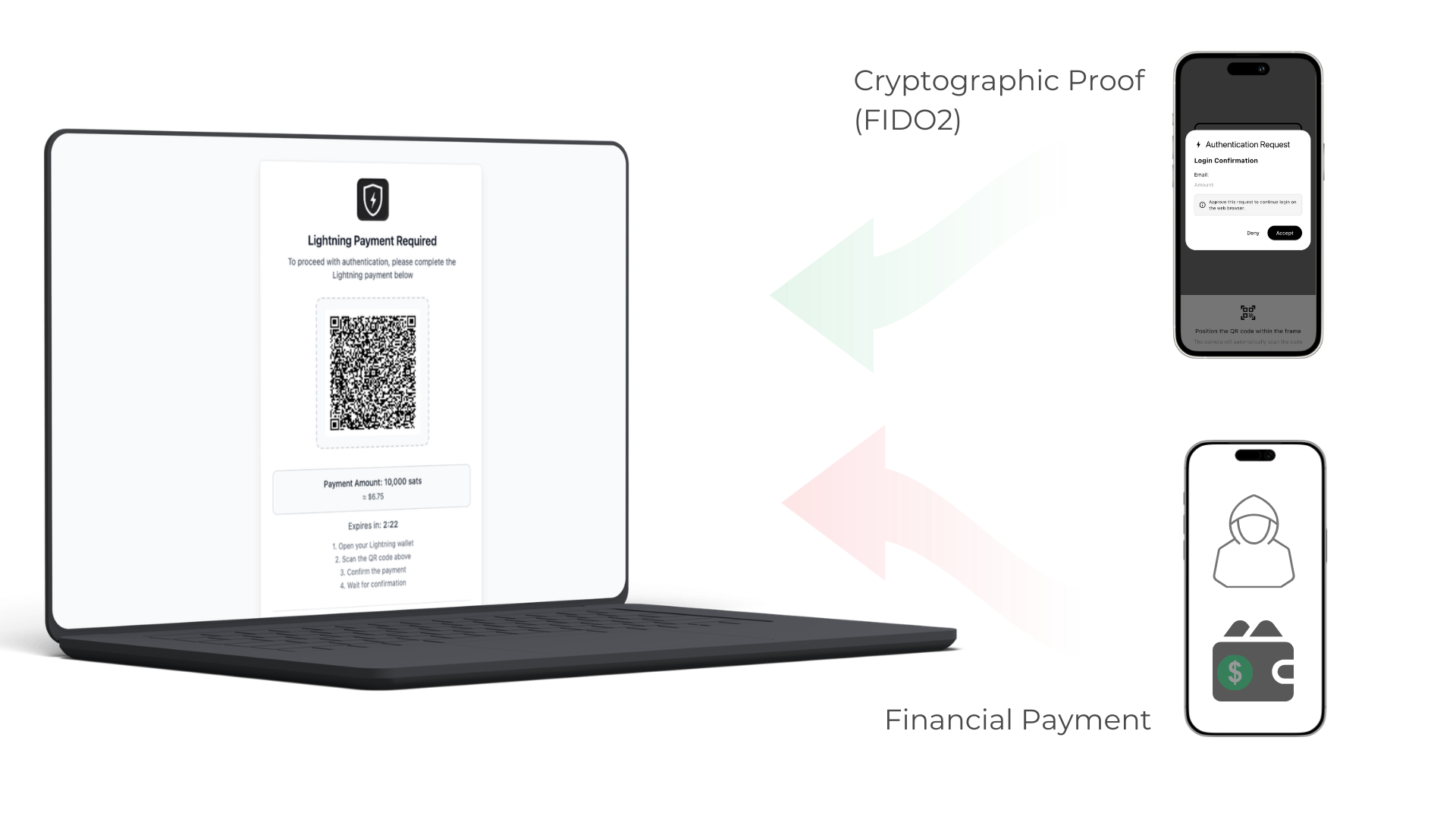
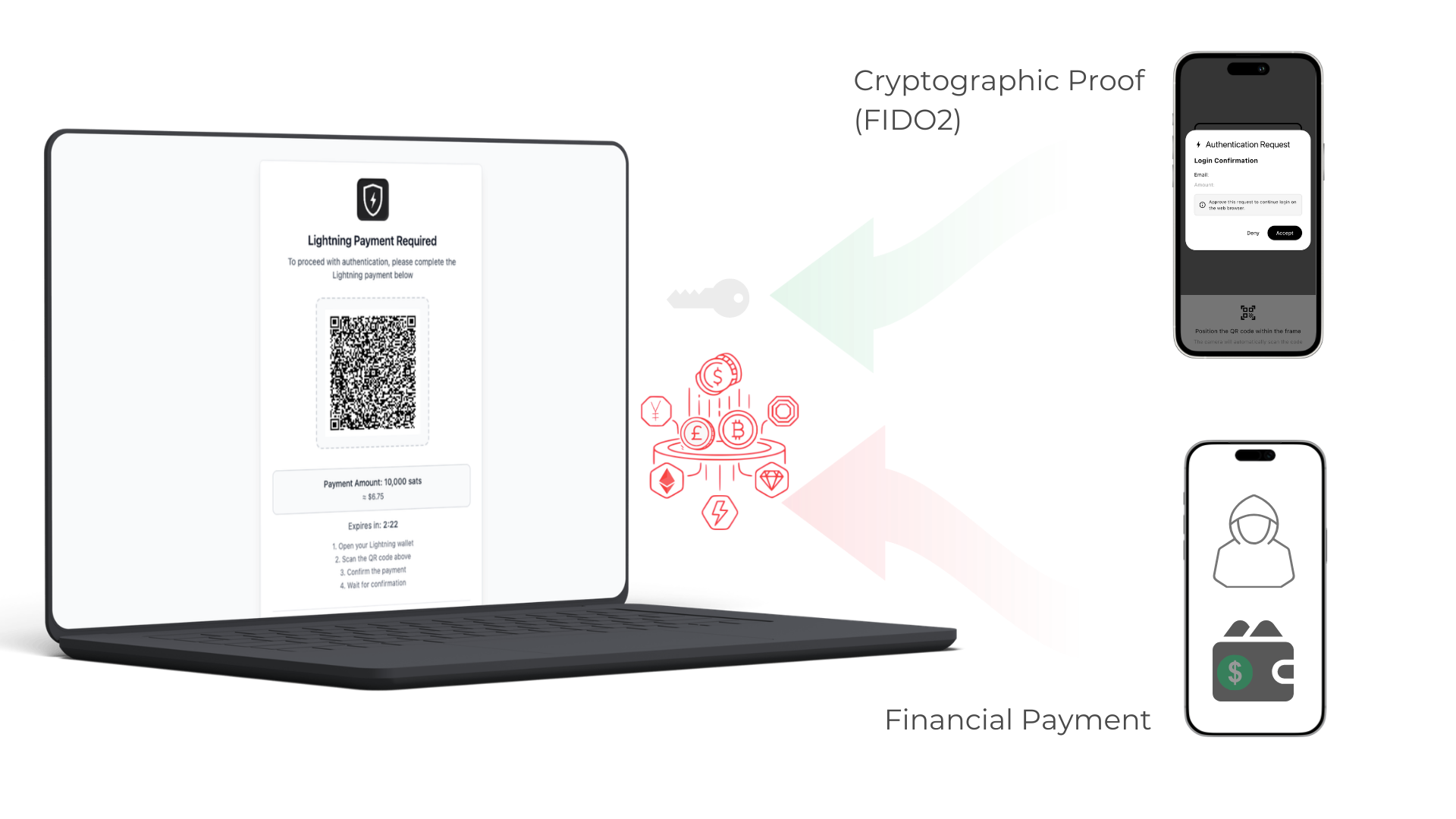
Smart Contract–Enforced Authentication
AuthLN places a programmable Cryptographic-based smart contract in front of protected resources. Every login attempt must satisfy that contract before access is evaluated.
AuthLN treats access attempts as contract-governed events:
Authorized users satisfy the contract with cryptographic proof.
Unauthorized actors must satisfy it with capital.
How Works:
Device-bound FIDO2 passkeys act as payment
A valid hardware-backed passkey assertion satisfies the smart contract requirement without monetary transfer.
No shared secrets, no reusable credentials
The passkey proves possession of the paired device and clears the contract condition instantly.
Unauthorized attempts require economic commitment
If a valid passkey is not presented, the contract requires a Lightning Network micropayment to proceed.
Automation becomes economically bounded
Credential stuffing, brute force, and AI-driven probing can continue — but each attempt now carries enforceable cost.
Policy-controlled enforcement
Organizations can define when cryptographic proof is sufficient and when economic commitment is required.
Your IdP remains the authority. AuthLN becomes the enforcement layer.
AuthLN integrates directly with your existing identity provider, adding device-paired authentication and economic enforcement without disrupting current workflows.
Full OAuth 2.0 support
SAML 2.0 integration
Works with Okta, Microsoft Entra ID, Google, and Ping
Guided setup wizards for rapid onboarding
No directory migration or credential duplication
Overlay deterrence on existing MFA and Conditional Access

Seamless Identity Integration
Deploy in under an hour. No lift-and-shift. No identity replacement.
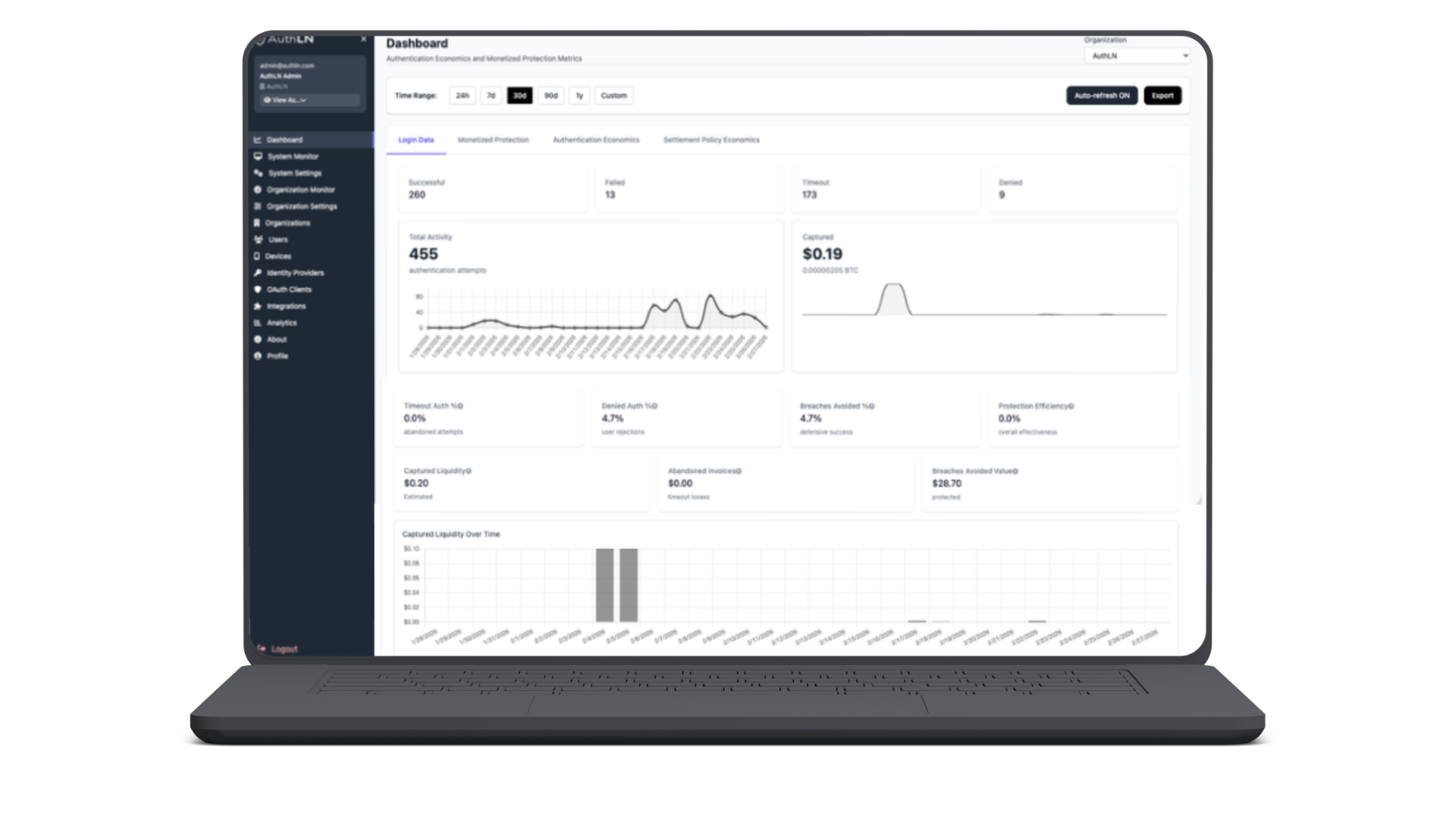
Every Event Becomes Signal
AuthLN captures every contract-governed authentication attempt — whether satisfied by cryptographic proof or economic commitment.
When access attempts carry consequence, security teams gain clarity.
Traditional systems generate logs.
AuthLN generates signal.
There are no silent probes. No anonymous retries. No discarded noise.
Every login attempt is recorded as an attributable event
Failed smart contract conditions generate high-confidence signal
Economic commitment amplifies intent detection
Eliminates background authentication noise
Transforms attack traffic into measurable telemetry
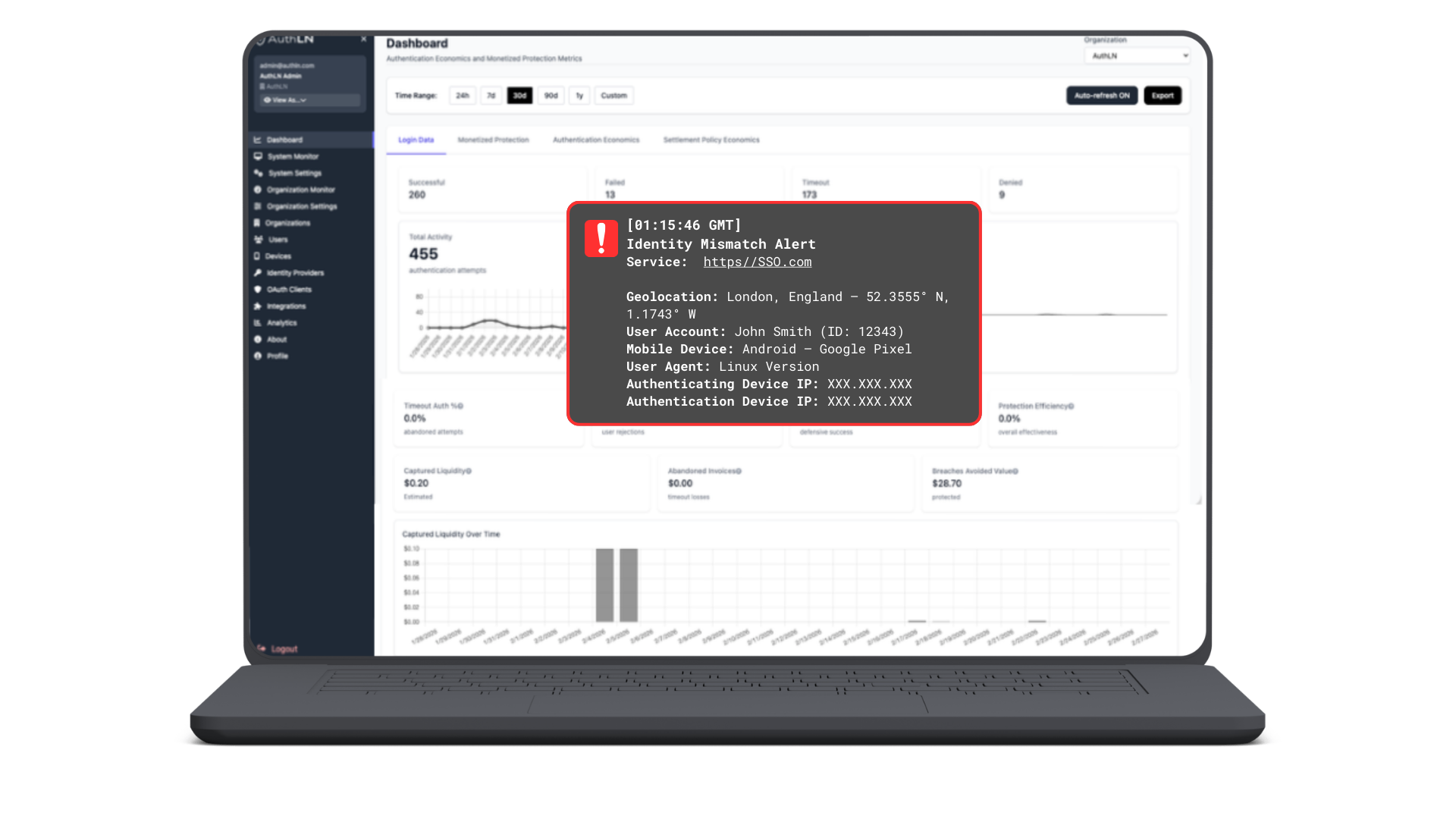
Pre-Breach Intrusion Alerts
AuthLN monitors every contract-governed authentication attempt. When a login attempt fails to satisfy the required cryptographic or economic commitment, your security team is alerted — before access is evaluated, before a session is created, and before your system is touched.
This is signal before breach — not incident response after damage.
Alerts triggered when required smart contract conditions are not met
Detects probing, automation, and incomplete payment attempts
No need to wait for account lockouts or MFA fatigue signals
Actionable telemetry tied to economically bounded events
A New Identity Factor
Authentication is no longer just what you know or what you have. It is what you commit.
AuthLN introduces an enforceable identity factor based on commitment.
Authorized users satisfy the contract with a FIDO2 passkey
Unauthorized actors must satisfy it with capital
Every attempt becomes attributable and economically bounded
Risk signals are amplified when attackers are forced to commit value
